¶ Frequently Asked Questions
This page is a work in progress. Questions are grouped into four sections:
¶ General Client FAQ
¶ What platforms is Polynom available on?
Polynom is available on Windows 10+, Linux (Debian 12+ or equivalent), macOS, Android 9+, and iOS.
¶ What is the Demo Server?
The Demo Server at demo.polynom.app is a publicly accessible server provided for testing and orientation. Users on the Demo Server are fairly restricted by default. Polynom is designed to be self hosted, so the Demo Server is not intended for regular use.
¶ Is Polynom free?
Polynom Community Server is free for individuals and small businesses. See the Welcome page for more information on available versions.
¶ What is a .nom file?
A .nom file is an exported Identity file. When you export your Identity from Polynom, it is saved as a password protected .nom file that can be imported on any device running Polynom.
¶ Are there limits on messages and attachments?
Attachment size, file upload size, the number of attachments per message, and the maximum number of characters per message are all determined by the Roles assigned to your Identity on a given server. Limits vary between servers. Contact a Server Admin or a User with the Manage Roles Permission if you need your limits adjusted.
¶ How do I leave a server?
Right-click the server button in the Toolbar and select Unlink to unlink the Server from your Identity. To completely remove the Server from your client, open the Servers page in Settings, right-click the Server and press Remove Server.
¶ Will I lose any data by updating Polynom?
No. Your data is tied to your Identity. As long as you have access to your Identity, your data is safe.
¶ What does Missing Permissions mean?
When you see a Missing Permissions message, the Role or Roles assigned to your Identity do not have the relevant permission enabled. Contact a Server Admin or a User with the Manage Roles Permission to have it enabled.
¶ What does Limit Exceeded mean?
When you see a Limit Exceeded or Invalid Limit message, your action has exceeded the limit set by the Role or Roles assigned to your Identity. Contact a Server Admin or a User with the Manage Roles Permission to have it increased.
How do I encrypt my client database?
¶ Identities and Graphatars
How do I import an existing Identity?
How many possible Graphatars are there?
¶ Can I have multiple Identities?
Yes. Polynom supports multiple Identities on a single device. Each Identity has its own Graphatar and can be switched between at any time from the Toolbar. New Identities can be created or imported from the Identities page in Settings.
¶ Can i use the same Identity on multiple devices?
Yes. Export your Identity as a .nom file from one device and import it on another. See Managing Your Identity for instructions.
¶ What happens if I lose my Identity?
If you lose your Identity and do not have a backup .nom file, it cannot be recovered. It is strongly recommended that you export and securely store your Identity as soon as you create it. See Backing Up Your Identity for instructions.
¶ Channels, Rooms and Features
What is the difference between a Channel and a Room?
What are Saved Messages and Sticky Notes?
¶ How do I join a server?
See Joining a Private Server in the Client Quick Start guide.
¶ How do I create a server?
See the Server Quick Start guide.
¶ Linux
¶ How do I enable the tray icon on Gnome desktop?
Many Linux distributions do not have app indicators enabled by default.
Debian based Gnome Desktop:
Install the app indicator extension:
sudo apt install gnome-shell-extension-appindicator
Reboot or log out and back in, then run:
gnome-extensions enable [email protected]
Red Hat based Gnome Desktop:
Install and run the Extension Manager:
flatpak install flathub com.mattjakeman.ExtensionManager
flatpak run com.mattjakeman.ExtensionManager
Enable the AppIndicator & KStatusNotifierItem Support extension.
The Polynom icon and menu should now appear in your system tray.
¶ General FAQ
What is Post-Quantum Cryptography?
What encryption algorithms does Polynom use?
What is Hiding in Plain Sight?
¶ Can Server Admins read my messages?
It depends on the Room type and whether Social Encryption is in use. In standard Chat Rooms and Announcement Rooms, Server Admins have access to content. Direct Messages are private and encrypted, and are not accessible to Server Admins. In Socially Encrypted Rooms, content is encrypted with a user controlled Social Encryption Key and is indecipherable to anyone who does not possess it, including Server Admins. Quantum Rooms go a step further by being completely invisible and inaccessible to anyone without the corresponding Social Encryption Key, meaning a Server Admin without that key has no way of knowing the room exists at all.
¶ What is the difference between Social Encryption and standard server encryption?
Standard server encryption is end-to-end encryption facilitated by the server between users. The server manages the keys involved. Social Encryption is a separate, user controlled layer of E2EE that sits on top of server encryption. Social Encryption Keys are derived from shared entropy known only to the participants, meaning the server has no knowledge of the key and cannot decrypt the content. See Social Encryption and Polynom Encryption for more detail.
¶ What is Self-Hosting?
Self hosting means running and maintaining your own server rather than relying on a third party server or cloud provider. With a self hosted server, you are responsible for the hardware, software, and security, and in return you have full control over your data.
This control is the foundation of data sovereignty: the right of individuals and organizations to determine whether their data is stored, how it is used, and who can access it. For teams with compliance requirements or a need for operational privacy, self hosting provides a level of control that no shared service can match.
Polynom Community Server is currently available for Linux. See the Server Quick Start to get started.
¶ Server FAQ
What port does Polynom Server use?
What is the difference between a Private and a Public server?
What is the difference between a Trusted and Untrusted server?
How does the Whitelist and Blacklist work?
¶ What operating systems does Polynom Server support?
Polynom Community Server currently supports Linux (amd64 Debian 12+ or equivalent). See the Server Quick Start for installation instructions.
¶ How do I back up my server?
Stop the server and copy the following files from your Polynom directory to a safe location:
polynom_server.dbpolynom_server.db-shm(may not always be present)polynom_serverr.db-wal(may not always be present)
These files contain your entire server database. Store backups securely and repeat this process regularly.
¶ How do I enable mobile push notifications?
Start Polynom Server with the -g flag to enable the mobile push notification gateway. See Server Quick Start for the full list of startup flags.
¶ How many users can a Polynom server support?
This depends on your hardware and configuration. If you are running a server with a large number of concurrent users, consider increasing your system's open file limit before starting Polynom. See Startup Options for instructions.
¶ Can I run multiple Polynom servers on the same machine?
Yes. Use the -p flag to assign each instance a different port number. Make sure each port is open in your firewall and forwarded from your router if hosting from home.
¶ VoIP FAQ
¶ Are VoIP call encrypted?
Yes. Every call on Polynom is end-to-end encrypted, facilitated by the server. If you are concerned about server level access to call content, adding a Social Encryption Key to your Call Room wraps the existing server controlled E2EE with a second, user controlled layer of E2EE. The server has no knowledge of the call content, and call quality is unaffected.
Polynom's cryptography is post-quantum, DPI resistant, and future proof.
(See also: Hiding-in-Plain-Sight™, Social Encryption™)
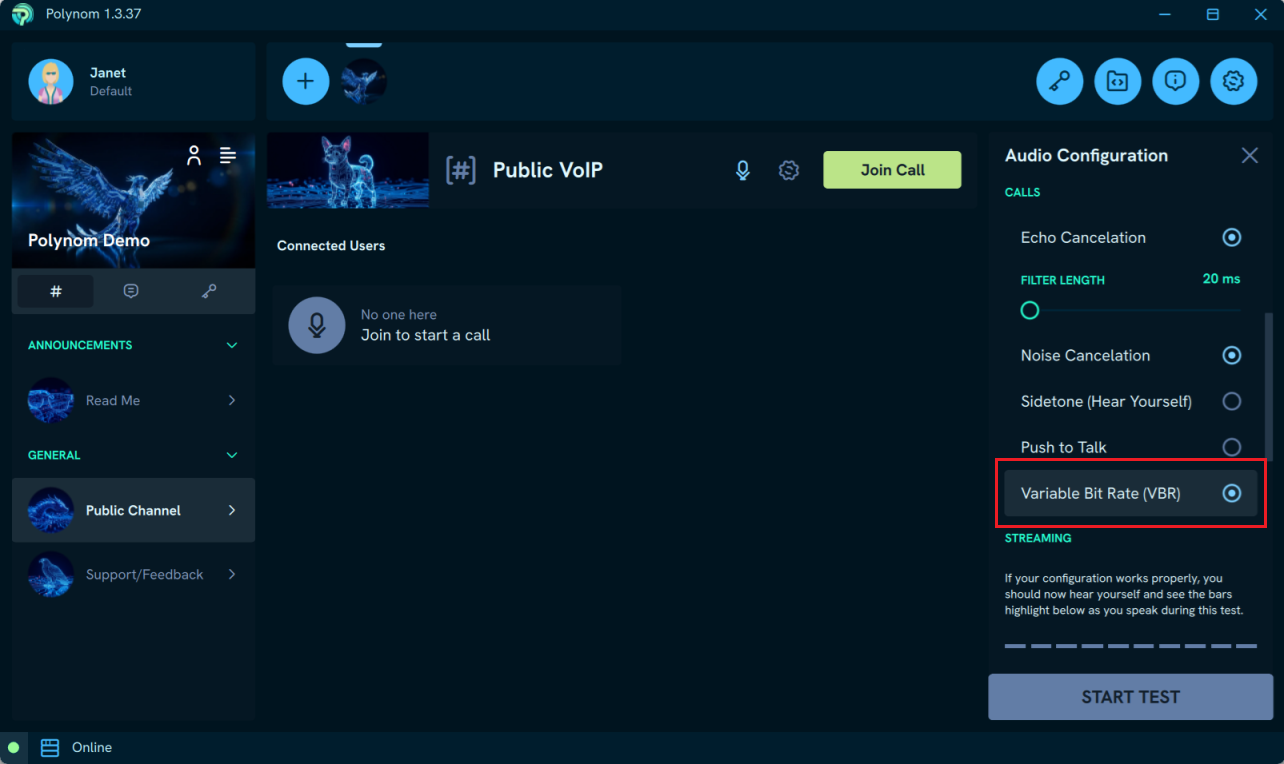
¶ Why or when might I want to disable VoIP Variable Bit Rate (VBR)?
VBR makes calls more efficient by transmitting smaller packets during quieter moments. This is the default setting. If you have reason to believe your encrypted calls may be subject to traffic analysis, disabling VBR in your client settings will cause Polynom to always transmit packets of the same size, making it impossible to determine when you are speaking from packet analysis.
¶ I'm having audio issues in a call
See the Troubleshooting section of the Voice Chat page for step by step guidance on resolving common audio issues, including problems with output devices, input devices, and per-user volume settings.